What technology should be in your cybersecurity stack? This is the question businesses are asking themselves with increasing concern as the cybersecurity environment continues to be a volatile and often dangerous place for organizations today.
Prior to the pandemic, cybersecurity was a big issue among organizations, many of which are seeing a rise in attacks every year. This has led to increased interest and investment in business security tools and solutions.
It’s becoming clearer with each and every year that having a scattered, incomplete, or piecemeal approach to your cybersecurity posture isn’t good enough for a modern strategy.
It’s not enough to just have a quality antivirus or VPN—businesses need to adopt a multi-layered strategy to fully protect themselves.
In this blog post, we’re going to take a look at the specific solutions that make up a quality cybersecurity stack.
For a deeper look into the threats that cybersecurity professionals work so hard to defend against, check out Impact’s webinar, Dissecting Cybersecurity Breaches: How They Happen & How to Stop Them.
The Necessity of a Cybersecurity Tech Stack
A modern cybersecurity program depends on more than a single control or point solution. As organizations adopt cloud services, support distributed workforces, and integrate third-party systems, their attack surface expands in ways that cannot be addressed by one tool alone.
A cybersecurity tech stack brings together complementary technologies that cover prevention, detection, response, and recovery, creating layered protection across users, devices, networks, and data.
A well-designed stack reduces blind spots by allowing tools to share context and reinforce one another. Endpoint detection can inform identity controls, network monitoring can validate anomalous user behavior, and centralized logging can surface patterns that would otherwise go unnoticed.
This integration improves both security outcomes and operational efficiency, helping teams move faster without sacrificing visibility or control.
Just as importantly, a defined tech stack supports consistency and scale. Standardized tools and integrations make it easier to apply policy, automate routine tasks, and adapt to new threats as they emerge.
Rather than reacting to incidents with ad hoc fixes, organizations with a cohesive cybersecurity stack are better positioned to manage risk proactively and align security efforts with broader business goals.
Employee Cybersecurity Awareness Training
By far the most significant attack vector used by cybercriminals is social engineering—71% of IT professionals say they’ve had employees at their company fall victim to these types of attacks.
A 2024 survey found that, for 90% of midsize and large companies, just one hour of downtime exceeds $300,000, with 41% reporting losses between $1 million and $5 million per hour.
The average cost of a social engineering data breach is around $4.1 million—untenable for many SMBs. Preventing costs like these by guarding and monitoring devices used frequently by employees is a key method of ensuring business security.
The vast majority of solutions in a cybersecurity stack will be geared towards minimizing cyber risk—through things like employee awareness training, powerful password policies, and email filtering, organizations can simultaneously protect their network, and their staff.
The Cybersecurity Stack
Now, we’re going to take a look at what you should expect in a cybersecurity stack.
We’ll be examining all the components of a cybersecurity stack—each tool and solution, what they do, what they protect, and why they are necessary for cybersecurity.
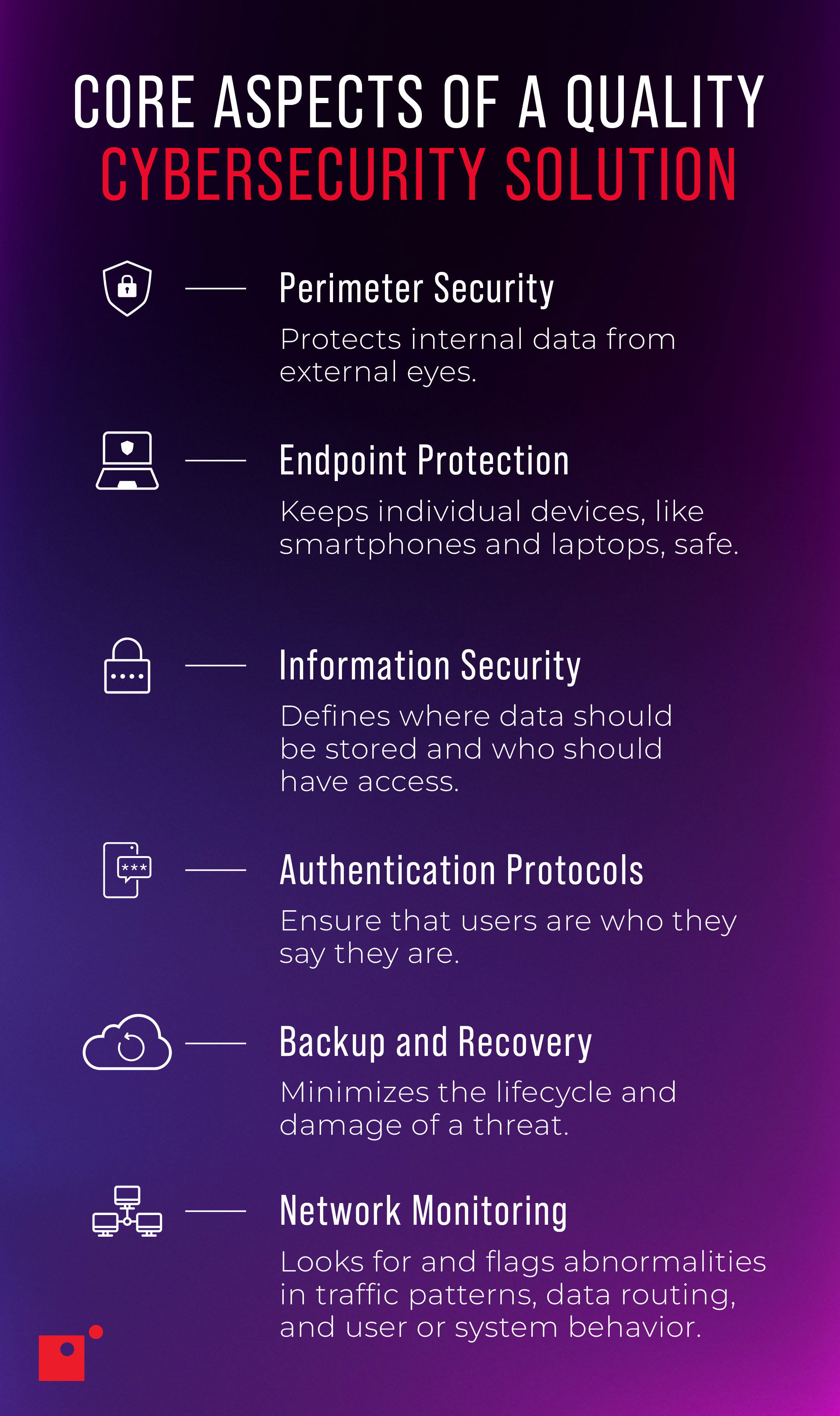
Perimeter Security
Perimeter security solutions protect data between a private internal network and an external public-facing network.
In short, it’s a protective shield for your business.
Traditionally, perimeter security has been the end-all, be-all of network security. Once upon a time, back in ancient days (the 2000s-2010s), it was often sufficient for companies to use just a perimeter firewall solution.
Now, that’s not the case today, but perimeter security still plays a vital role in securing data internally for businesses.
There are several solutions that can achieve this. The most notable are unified threat management and a web application firewall.
Unified threat management (UTM) is a comprehensive solution that includes a lot of tech that you’re likely already familiar with. Antivirus; firewall; intrusion detection; spam filtering; content filtering; and, in some cases, VPN support for encrypted communications.
UTM is an excellent tool for uncovering and nullifying potential threats attempting to gain access to your network.
A web application firewall, or WAF, is similar, but focuses on data traveling between the end user and any cloud apps they’re using. Because so many businesses today store, handle, and access data in the cloud, WAFs have become important tools to supplement cybersecurity strategies.
Endpoint Protection
Just as WAFs are more significant today because of the increased use of cloud apps in organizations, endpoint protection is also important because of the modern prevalence of the Internet of Things (IoT), which has led to a substantial increase in the number of devices businesses have to protect and monitor on their network.
Endpoints are everywhere in a modern business environment—smart TVs, mobile devices, printers, vending machines, you name it. Smart tech and operational tech are creating completely new branches of cybersecurity.
To manage these endpoints, businesses should utilize domain name system (DNS) protection. DNS is best thought of as a sort of “phonebook” for computers, which logs IP addresses rather than phone numbers.
Of course, not every “number” or site in the phonebook is trustworthy and there are many malicious sites out there. DNS protection stops access to malicious sites and can be extended to all devices under a network, meaning an employee browsing on their phone using your company network won’t accidentally let a threat actor into your network by visiting a dangerous website.
Cisco has indicated that over 90% of attacks are done via DNS and only two-thirds of organizations monitor their DNS records.
Then we have managed detection and response (MDR), which is an endpoint protection service that detects, prevents, and responds to attacks across all vectors.
As opposed to searching for the characteristics of malware—which can be hidden or changed to something unrecognizable—as a traditional protection service would, MDR monitors the processes of every endpoint, recognizing deviations from the norm and responding.
Finally, we have persistence detection. “Persistence” refers to a modern hacking process whereby cybercriminals gain access to your systems and wait for the opportune moment to strike by lingering silently in the background undetected.
This solution uses advanced technology to sniff out bad actors hiding in plain sight by collecting information and activity associated with persistent mechanisms that evade other cybersecurity technologies.
Information Security
Information security is essential in preventing data leakage and other forms of unintentional data loss.
Information security is all about access and stopping inadvertent data loss. Data loss prevention (DLP), for example, is about preventing data leakage, which refers to the unauthorized transfer of data from inside your organization to outside.
DLP aims to rectify this issue by establishing clear standards for your data through labeling and categorizing. This means determining where certain data should be stored, who has access to it, and where it can be shared.
This approach is a typical standard in cybersecurity programs and avoids the significant issues that data leakage can bring to a business.
Email protection, meanwhile, operates on the same premise; only for your email communications. Email protection solutions help prevent many common cyberattacks like phishing attempts and other social engineering scams.
Authentication Protocols
Authentication solutions ensure the people accessing your business data are who they say they are.
Authentication is a simple and incredibly effective way of preventing unauthorized users from accessing your business data, and yet is not taken seriously and often overlooked by companies in their security policies.
Microsoft estimates that using MFA stops 99% of all automated brute force attacks.
Multi-factor authentication (MFA), which requires the use of a secondary device or method to authenticate a user, has proven especially useful in preventing breaches. Solutions that cater to this are capable of protecting every app or software service you use in addition to meeting modern compliance standards.
Likewise, automated password management solutions mean that you can ensure your employees are consistently staying up-to-date with strong passwords.
This tech can push password change automation, keep a full trail of password history, and encrypt all the information tracked.
Backup and Disaster Recovery
In case of a data disaster, businesses need to retrieve lost information as soon as they possibly can.
Backup and disaster recovery (BDR) solutions are aimed at making sure that any vulnerable information in your business, whether that’s data stored on internal servers, external cloud data, or website data, is backed up and can be restored instantly.
BDR is a way of preparing for the worst, because data breaches can be incredibly costly to SMBs.
The average time it takes for a company to identify and contain a data breach in their system is 279 days—that’s over nine months.
The issue is that many businesses do not have any form of BDR in place, making this an important part of any cybersecurity strategy.
Then we have a software-as-a-service backup, which protects the data that people handle on their cloud apps, as well as website backup, which restores all data from your website in the event of a breach.
Network Monitoring
Last, but by no means least, the final component of a cybersecurity stack is monitoring.
Monitoring tools provide total visibility into your network and help you pinpoint vulnerabilities.
These tools include vulnerability scanning, security information and event management (SIEM), and network detection and response (NDR).
Vulnerability scanners use machine learning to automatically assess risks associated with functions and processes across your hybrid network—whether on the cloud or on premise and hardwired.
When vulnerabilities are detected, they are prioritized in terms of their threat level and patched to ensure safety.
SIEM is a monitoring and event management solution that can be integrated with several major tech providers like Microsoft. This solution will alert you if it recognizes, for example, a suspicious login or excessive failed login attempts, in addition to general instances of abnormal behavior across your network.
The SIEM effectively creates a centralized database of any and all threats and abnormalities discovered by the solution, escalating them to your IT team in real-time for remediation.
Network detection and response (NDR) is similar but is more focused on network traffic analysis (NTA) detecting anomalies and providing more granular data on security events that raise suspicion.
A managed network security monitoring service helps businesses increase their visibility into their network profiles, offering a more extensive approach to threat detection than SIEM alone.
The Reality of Evolving Threats
Threat actors continue to adapt faster than traditional security models were designed to handle. What were once isolated incidents have become sustained campaigns that blend phishing, credential abuse, ransomware, and supply chain compromise.
These threats are no longer limited to large enterprises or highly regulated industries; they target any organization with valuable data, operational dependencies, or limited security resources.
The pace of change is driven by automation and accessibility, largely due to AI. Attack tools are cheaper, easier to use, and widely shared, allowing less sophisticated actors to execute effective attacks at scale. At the same time, organizations are managing more identities, more endpoints, and more cloud-based assets than ever before, creating complexity that attackers actively exploit.
This evolving threat landscape requires security strategies that are dynamic rather than static. Controls must be continuously updated, signals must be correlated across environments, and response must account for both speed and impact.
Recognizing the reality of how threats evolve is a prerequisite for building defenses that can hold up under real-world conditions.
Wrapping up on Cybersecurity Stacks
We hope that by reading this blog post you now have a greater understanding of what a comprehensive cybersecurity strategy looks like for a modern business.
At Impact, we always recommend a layered approach to cybersecurity that covers all your bases.
It’s unfortunately no longer the case that a simple firewall—or any one solution for that matter—will be sufficient for any organization’s cybersecurity posture.
In order to protect yourself to the fullest degree and avoid costly data breaches, consider conducting a cybersecurity audit, and identifying where some of these network security tools and solutions can bolster your posture.
For more on how cybersecurity professionals are working alongside cutting edge technology to defend business networks, check out Impact’s webinar, Dissecting Cybersecurity Breaches: How They Happen & How to Stop Them.