When you think about cybersecurity measures like managed detection and response (MDR), it’s helpful to think about it like a physical security system. For instance, a bank has several layers of security from the vault door, to the alarm systems, the under-desk panic buttons, and of course, security cameras. In cybersecurity, managed detection and response functions like the security cameras in the bank.
The same way the security cameras constantly monitor the premises of the bank, managed detection and response is a specific arm of cybersecurity responsible for continual network monitoring, threat hunting and identification, and remediation protocols.
By investing in a sophisticated MDR strategy, organizations can greatly reduce the amount of time it takes to discover, isolate, and neutralize cyber threats across the network, in turn, preventing high-cost incidents.
The line between IT and cybersecurity is thin and often hard to define. Check out Impact’s webinar, The Difference Between IT and Cybersecurity Standards to learn how you can differentiate and better allocate responsibilities appropriately.
How MDR Works
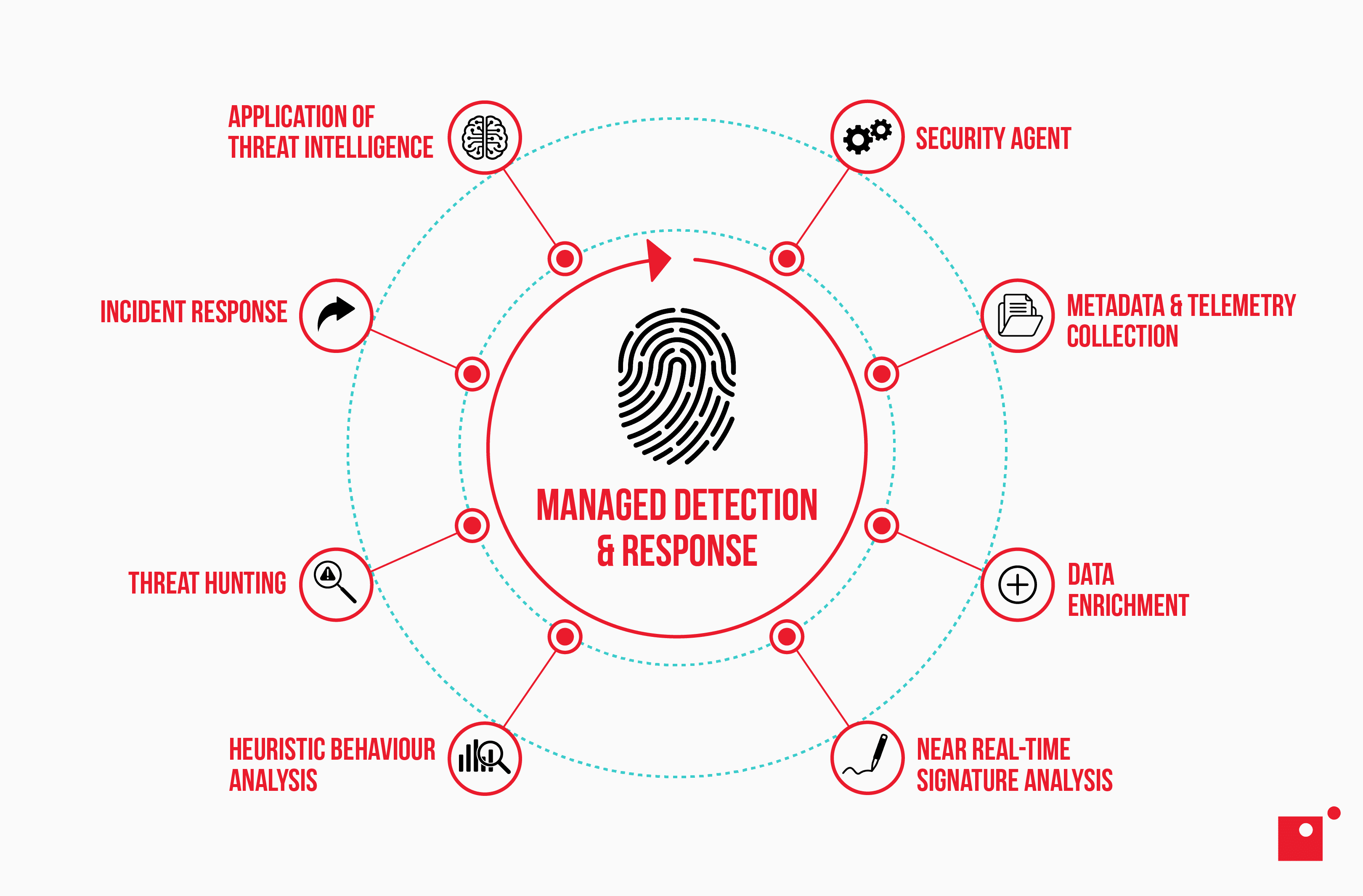
Managed detection and response is a cybersecurity service designed to identify and respond to advanced cyber threats. Unlike traditional security measures, MDR goes beyond mere prevention, focusing on continuous monitoring, detection, and swift response.
MDR operates on a proactive model, constantly analyzing network activities and endpoints for any signs of malicious behavior. Advanced threat detection technologies, including machine learning and behavioral analytics, form the backbone of MDR services. These technologies enable the system to recognize patterns indicative of potential threats, even in the absence of known signatures.
Once a potential threat is detected, MDR takes immediate action. This can involve isolating affected systems, blocking malicious activities, and initiating incident response procedures. The goal is not just to prevent an ongoing attack but to understand its scope and neutralize it at its root, if possible.
The processes that are involved in a typical MDR plan include:
- Proactive threat hunting and network monitoring
- Security alert prioritization
- Incident investigation
- Remediation
Let’s take a quick look at each with a little more detail.
Proactive Threat Hunting and Network Monitoring
Proactive threat hunting involves actively searching for potential security threats before they manifest into full-fledged attacks.
This element of MDR is about keeping your network defense systems one step ahead by employing advanced techniques such as anomaly detection, behavioral analytics, and continuous network monitoring.
Anomaly detection in MDR involves monitoring network and system activities to identify unusual patterns or behaviors that may indicate potential security threats. It helps in detecting previously unseen or unknown threats by flagging deviations from established norms.
Behavioral analytics is used to establish a baseline of normal behavior for users, devices, and systems. Deviations from this baseline, such as unusual user activity or abnormal data access patterns, can be indicators of potential security incidents.
Continuous network monitoring is the ongoing, real-time surveillance of network activities to identify and respond to security threats promptly. This involves monitoring network traffic, logs, and other relevant data sources continuously to identify suspicious activities, vulnerabilities, or signs of compromise in real time.
Security experts use monitoring tools to constantly scan network activities, endpoints, and activity logs to identify subtle signs of malicious threats like abnormal user behavior or deviating data patterns, ensuring threats are discovered early in their lifecycle so they can be neutralized.
Security Alert Prioritization
In the vast sea of security alerts, not all signals are of equal importance. Security alert prioritization is a critical aspect of MDR that involves categorizing and ranking alerts based on their severity and potential impact.
Let’s say you’re making a roast and want to have a salad as an appetizer. Your main priority is going to be cooking the roast since it needs more time, while the salad can be tossed just five minutes before eating. If you don’t have your priorities in the right order, your whole meal is ruined, or at least significantly delayed.
This is why alert prioritization is such a vital aspect of effective MDR strategies.
Through the use of threat intelligence and contextual analysis, MDR services ensure that security teams focus on addressing the most dangerous threats first. This prioritization streamlines the response process, allowing organizations to allocate resources efficiently and respond to the most critical security incidents in a timely manner.
Incident Investigation
When a security incident occurs, thorough investigation is integral in understanding its scope, origin, and potential impact. MDR services excel in Incident Investigation by employing a combination of automated analysis and human expertise.
Security professionals delve into the details of an incident, tracing the attacker's footsteps, and gathering forensic evidence. This investigative process not only aids in containing the current threat but also informs future security strategies to fortify defenses against similar attacks.
Remediation
Remediation is typically the final element in a standard MDR lifecycle.
Once a threat is detected and investigated, swift action is taken to neutralize and eradicate it from the system. Remediation strategies can include isolating affected systems, applying software updates or patches, updating security configurations, and blocking malicious activities.
MDR services paired with cybersecurity experts provide invaluable insight into proper remediation tactics, ensuring that organizations not only respond to incidents effectively but also implement measures to prevent similar threats in the future. This proactive approach minimizes downtime, data loss, and potential damage caused by cybersecurity incidents.
Managed Detection and Response Benefits
The advantages of implementing managed detection and response protocols are multifaceted. One of the primary benefits is the ability to detect and respond to threats in real time. This proactive approach significantly reduces how long threats within an environment go undetected, known as dwell time, minimizing the potential total damage.
MDR also offers a level of expertise that many organizations may lack internally. Cybersecurity experts, armed with the latest threat intelligence, continuously monitor and analyze data to stay ahead of emerging threats. This level of vigilance ensures that organizations have powerful defenses against even the most sophisticated attacks.
Another key benefit is the scalability of MDR services. As an organization grows, so does its attack surface. MDR can seamlessly adapt to changing environments, providing consistent and effective protection regardless of the organization's size or complexity.
Where MDR Fits Into an Overarching Cybersecurity Strategy
In the grand scope of cybersecurity, MDR serves as a crucial thread, weaving its way through various layers of defense. While traditional security measures like firewalls and antivirus software focus on preventative and reactionary measures, MDR is specifically designed to be a proactive defense system.
MDR complements existing security infrastructure by filling gaps and addressing blind spots. It works hand in hand with endpoint protection, network security, and other cybersecurity tactics to create a holistic cybersecurity strategy. This integrated approach ensures that threats are tackled from multiple angles, leaving little room for malicious actors to exploit vulnerabilities.
Furthermore, MDR plays a vital role in incident response planning. In the unfortunate event that a security incident does occur, MDR will rapidly identify, isolate, and neutralize the threat, minimizing damage and downtime.
This near-instant response not only protects sensitive data but also helps organizations maintain trust with their customers and stakeholders.
How AI Is Evolving MDR
AI is making managed detection and response faster and smarter by improving how threats are spotted and stopped. Traditional MDR relies on human analysts to comb through the data to catch and respond to threats, which can take time.
AI changes the game by analyzing large amounts of data in real time, quickly and more accurately spotting unusual activity that could signal a cyberattack. It helps MDR systems adapt to new threats as they emerge, reducing false alarms and improving the response overall.
AI also helps MDR anticipate attacks before they happen by using historic threat signatures and comparing them to new activity. This allows security teams to fix weaknesses before they’re exploited. AI-powered systems can even step in automatically—isolating compromised devices, stopping the spread of threats, and starting recovery within seconds.
This makes AI-driven MDR a powerful tool for staying ahead of increasingly complex cyberattacks.
Wrapping Up on Managed Detection and Response
Managed Detection and Response is not just a service; it's a proactive strategy that helps protect against the ever-evolving landscape of cyber threats. By combining advanced technologies with human expertise, MDR offers a robust defense mechanism that goes beyond traditional reactive cybersecurity tactics.
As organizations navigate the complex realm of cybersecurity, integrating MDR into their strategy becomes not only a choice but a necessity. The benefits of real-time threat detection, expert analysis, scalability, and seamless integration make MDR a formidable ally in the ongoing pursuit of digital security and resilience.
If you’re relying on your IT team for network security practices, it might be time to think about establishing a separate team for your cybersecurity needs. Learn more about the difference in Impact’s webinar, The Difference Between IT and Cybersecurity Standards.