The evolution of cybersecurity came about swiftly and suddenly. After the dawn of the internet, it was immediately clear that this infinite space we developed was going to need some guardrails. These guardrails became the framework for cybersecurity practices which are still evolving today.
To understand how we got to the current cybersecurity landscape, we need to look back in time. Learning from the past reveals our progress, uncovers powerful insights, and helps us prepare for the future while avoiding repeat mistakes.
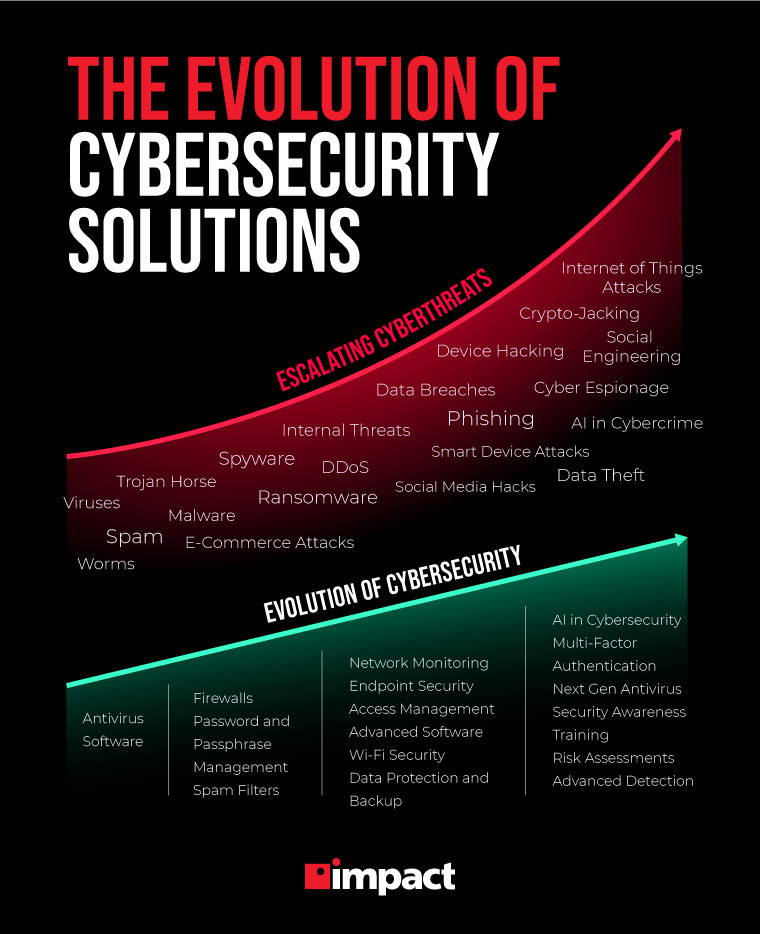
Below, we comb through the history of cybersecurity, review the modern cyberattacks threatening businesses today, and discuss strategies businesses can use to mitigate their cyber risk now, and in the future.
Cybersecurity and IT network security have a lot in common but are two distinct fields from one another. Learn about their differences and what you need to address both these practices in Impact’s webinar Modern Business Requirements: The Difference Between IT and Cybersecurity Standards.
The Beginning of Cybersecurity
A long time ago in technology’s past, the first-ever cyberthreats began to rear their ugly heads as the computer began to make its mark on the world. The precursor to the internet was ARPANET which enabled computers to talk to one another over long distances without a dedicated phone line. A huge technological milestone, and one step closer to the internet.
It was on this early beta-esque version of the internet that the first ever computer virus, Creeper, made its debut.
Creeper was a program that bounced from machine to machine, eventually self-replicated, moved across networks, and taunted users with a message reading, “I’m the creeper, catch me if you can!” This type of malware is now known as a worm and modern versions can cause serious damage to your network.
However, Creeper was far from the malicious programming we see in today’s cyberthreats like ransomware, spyware, or data sapping malware. Rather, it was mainly an experiment ran by scientist Bob Thomas to demonstrate the possibility of the coding.
In fact, Creeper wasn’t even able to self-replicate until Thomas’ colleague, Ray Tomlinson, enhanced the programming. Ironically, it was also Ray Tomlinson who then created Reaper, the world's first anti-virus specifically designed to hunt down Creeper.
Just like that, the world of cybercrime and cybersecurity was created – and the ceaseless battle between good and evil entered the digital universe.
Reviewing the Evolution of Cybersecurity
As computers became more powerful and ARPANET gave way to the internet, more and more businesses and individuals adopted its use. Eventually the need for security became more apparent as more viruses and cyberthreats surfaced.
In 1987, the next major innovation in cybersecurity came from John McAfee in the form of the first major antivirus software in the United States.
These cybersecurity innovations came at almost the perfect time, too. The ’90s would become known as the “Virus Era” because millions of computers got infected with malware during the first decade of the internet.
During this time, firewalls and antivirus software were the main sources of security. These preliminary cybersecurity tools scanned incoming packets from the internet for malware and deployed immunizer to neutralize them. An immunizer is a tool that modified programs on the drive to trick viruses into thinking they were already infected with malware. This stopped the virus from actually infecting programs on the system.
In the 2000s, cybercrime became more prominent as more of the world entered the digital era. World governments began to recognize cyberattacks and the need for cybersecurity, and information security became a focus for businesses, people, and governments alike.
Modern Solutions to Face Modern Threats
Modern businesses are facing new cyber threats that are evolving to beat current cybersecurity systems and technology. To stay protected, businesses must have the latest tech, establish comprehensive cybersecurity strategies, and a team of cybersecurity experts to monitor and proactively defend your network.
Here’s a look at some of the key elements of a modern cybersecurity strategy:
- Remote Work Security: More people are working remotely than ever before, meaning that businesses need to take steps to ensure information is secure no matter where it’s being accessed. This means prioritizing endpoint security, creating a company device management policy, and keeping your staff educated on current cyberthreats they might face.
- Network Monitoring: Cyberattacks can come at any time from many different angles. Therefore, it’s critical that businesses have a network security monitoring service provider to identify, isolate, and neutralize threats. 24/7 monitoring is critical to keeping your network secured.
- Edge Security: With remote work, more smart-devices connect to the company network. Edge security helps ensure the security of the network all around the world, even if a device used by a remote worker is breached.
- Backup & Disaster Recovery: With so much data being stored on the cloud, a cyberattack can cripple systems and limit access to important information. Having backups and a recovery plan helps businesses get back up and running quickly.
- Access Management: Thanks to cloud computing, more people can access data, but to ensure security, businesses need to manage who can access what and from where. The more people who have access to sensitive information, the higher the vulnerability risk. Make sure that staff members only have access to the sensitive information they require to do their job.
Looking Ahead – Where the Cybersecurity Evolution is Going
Cybersecurity is constantly evolving because it has to. Cybercriminals are becoming more and more tech-savvy, using more sophisticated programming techniques, and are developing nastier and nastier malware each and every year.
Cybersecurity technology, strategies, and programming needs to advance as close to the same rate as possible, and ideally would be advancing faster than its cybercrime counterpart.
Future Cyberthreats
Cyberthreats are always changing as hackers look for new ways to penetrate systems. Here are some trends to watch in cybercrime:
- Ransomware Threats: Ransomware attacks are growing quickly and costing businesses $75 billion around the world with an average cost of $133,000. Because more sensitive (and valuable) information is being stored on the cloud, experts predict that ransomware attacks will continue to rise.
- Supply Chain Breaches: In 2021, attacks on the supply chain tripled. Hackers know they can devastate businesses with coordinated, targeted attacks on vulnerable parts of a supply chain and the amounts of money to be made by holding them hostage. Protecting the supply chain is going to be a focus for companies heading into the next few years.
- Cloud Attacks: Cloud technology brings many new challenges to defend against cyberattacks like encryption, access management, and backup and recovery plans. This paired with the fact that the cloud is growing 56% every year means that this could be cybersecurity’s next big battleground.
Future Cybersecurity Solutions
To defend against future threats, businesses will need to implement futuristic solutions. Simply installing an antivirus software and hoping for the best just isn’t enough in today’s sophisticated cybercrime market.
Here are some strategies and tools that help businesses future-proof themselves as the evolution of cybersecurity continues:
- Passwordless Authentication: Businesses are (or should) already be moving away from traditional password use, especially if their current method of password management is just to set one password and never change it. With new kinds of multi-factor authentication available, passwords may become a thing of the past or at least just a small part of a more complex login process.
- AI and Automation in Cybersecurity: The introduction of artificial intelligence has made cybersecurity smarter, faster, and better at recognizing the telltale signs of an attack by analyzing data and monitoring network use.
- Managed Cybersecurity Services: With so much to juggle between updating systems, implementing new technology, constant network monitoring, and performing consistent awareness training, businesses are right to feel overwhelmed. Enlisting the help of a managed security service provider (MSSP) like DOT Security can give businesses easy access to teams of specialists dedicated to protecting their data and helping to mitigate the risks of cyberattacks.
Partnering with an MSSP is also financially advantageous, as there’s a massive cybersecurity talent shortage and hiring a full cyber-security team in-house is extremely expensive right now.
Wrapping up on the Cybersecurity Evolution
Understanding the past helps prepare us for the future. Regarding the evolution of cybersecurity, one lesson we’ve learned that’s as old as time itself is to always expect the unexpected. Prepare for the worst and hope for the best, so to speak.
Unfortunately, there’s no universal cybersecurity solution that can protect any organization from cybercrime 100%. However, by going through the suggestions in this article, you can establish a comprehensive cybersecurity policy, outfit your network with updated technology and cybersecurity protocols, and ramp up your organization’s cybersecurity posture.
With the worldwide cybersecurity talent shortage, you might want to consider partnering with an MSSP for full cybersecurity coverage.
Explore the new evolutions of security technology, and how modern cybersecurity is different from traditional IT security, with Impact’s webinar Modern Business Requirements: The Difference Between IT and Cybersecurity Standards.