Car insurance rates are influenced by all sorts of factors, but one of the main determinants is the overall risk associated with you as a driver and the car being insured. A family mini-van is a lot less expensive to insure than a Ferrari.
Similarly, if you want to implement a thorough cybersecurity strategy, you need to understand the overall risk associated with your business and its current efforts. If you don’t know where your cybersecurity risk lies, you also won’t know where to focus your network security efforts.
If you’re curious about threat hunting and how professionals go about combatting cyberattacks, check out Impact’s webinar, Dissecting Cybersecurity Breaches: How they Happen & How to Stop Them.
What Is a Cybersecurity Risk Audit?
A cybersecurity risk assessment or audit takes a deep dive into the internal IT systems of a business to determine risks. This involves a combination of vulnerability scanning and penetration testing in order to pinpoint solutions and protocols that bolster the business’ security practices and keep itsafe from cyberattacks.
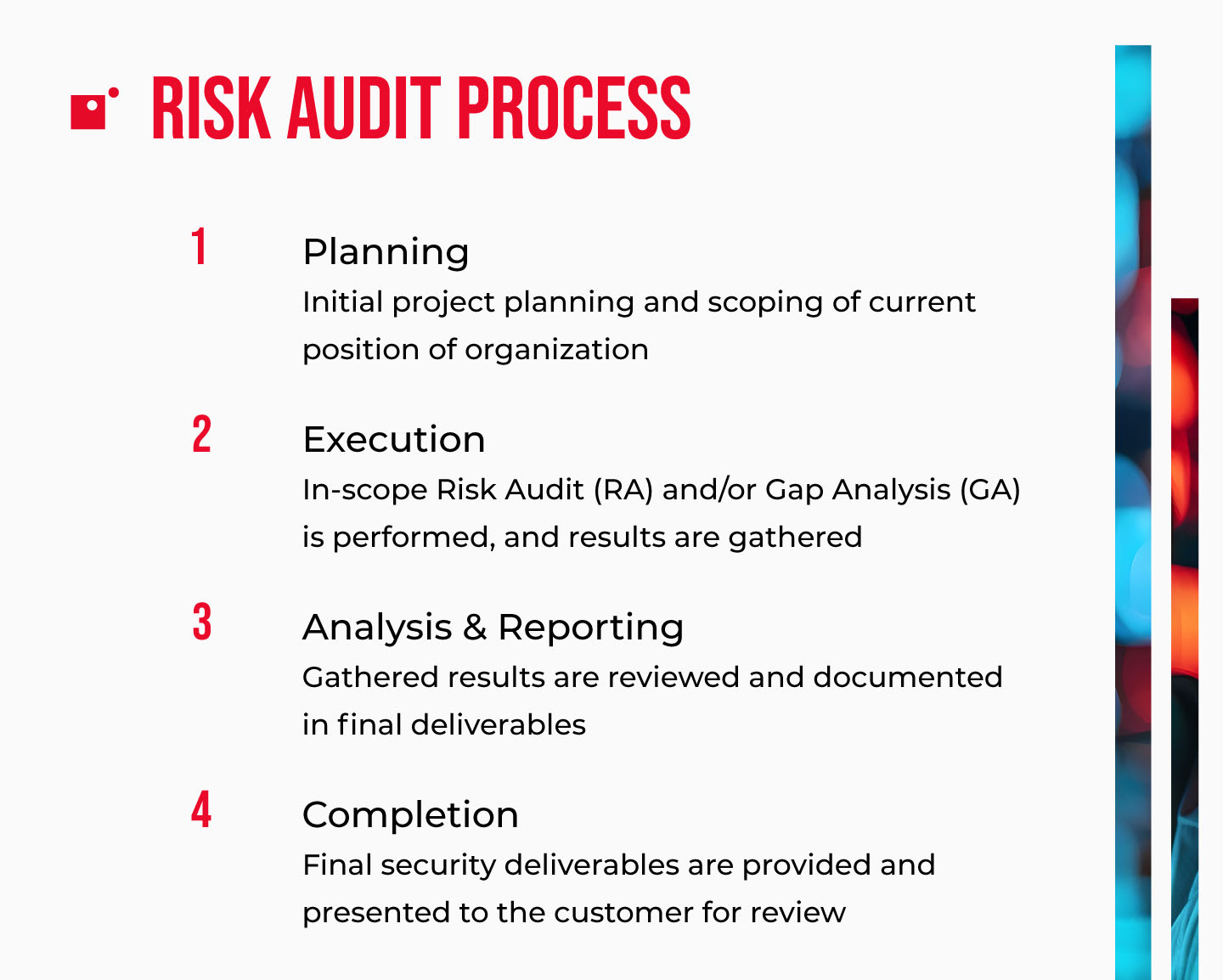
A comprehensive cybersecurity risk audit will provide you with a complete picture of your current cybersecurity posture through a systematic process that includes three phases:
- Plan
- Execute
- Analyze and Report
Why Impact Recommends Conducting a Cybersecurity Risk Audit
Cybersecurity has become such a major focus for businesses over the last few years that having cybersecurity insurance has become the norm rather than the anomaly.
“By the end of 2024, privacy regulation will cover three quarters of consumer data worldwide, but 60% of all regulated global entities will struggle to comply with intensifying data protection regulation and privacy requirements (Gartner), given the high rates of data growth driven by technology.”
Businesses frequently adopt solutions that can help them use their data. That means more of their information is frequently handled, processed, stored, and transferred; which generates opportunities for cybercriminals.
With so much data and so much data movement, there is more room for error and more attack vectors that need protection, ultimately creating more ways for cybercriminals to get their hands on your data and sensitive information.
Auditing your cybersecurity strategy, however, will help you fill gaps in your security with effective and proven solutions.
Let’s take a closer look at the three steps involved in a thorough cybersecurity risk audit, how they work together to help organizations understand their current strategy, and what solutions they can implement to substantially reduce their level of risk.
Step 1: Planning
The planning stage of an IT security risk assessment identifies a business’ obligations, expectations, and key personnel responsible for the project.
This means installing a process that clearly defines the project and how communication will flow between the key players involved in the audit. This is the point at which you need to designate the stakeholders, liaisons, and overall goals.
Auditors will also need access to the systems that live on your network, so you’ll need to gather all of the necessary information and credentials in preparation for the audit itself. The exact requirements will be defined by the auditors prior to the engagement, which should give you plenty of time to collect anything needed.
Then, the last step in the planning phase is getting the audit scheduled.
Step 2: Execution
The execution phase of the audit is where the real substance of this process gets flushed out.
This is when the risk audit team will begin testing and scanning the network. This helps the auditors understand the architecture of the network as well as the strength of the current cybersecurity measures already in place.
This is typically broken up into two distinct areas: vulnerability scanning and penetration testing, in addition to the optional gap analysis which can also be performed.
Vulnerability Scanning
When cybercriminals target businesses, their attack tactics will almost always follow the path of least resistance. In other words, the glaring weaknesses or obvious vulnerabilities existing somewhere on your network are much more likely to be targeted by an exploit.
By scanning your internal network for major vulnerabilities, the audit identifies cybersecurity weaknesses that would allow a threat actor to enter your network, make lateral movements, and compromise additional systems, accounts, or servers beyond the initial infiltration.
These scans map out your network and determine where you’re most vulnerable to attack.
Penetration Testing
Another pillar of a cybersecurity risk audit is penetration testing, which seeks to ethically and safely gain entry to your network by exploiting vulnerabilities. In other words, penetration testing makes use of the same tactics that threat actors lean on. This is a great way for businesses to test the cybersecurity solutions they put in place.
Penetration testing is performed by a cybersecurity professional who is familiar with malicious hacking practices and uses this knowledge to help businesses improve the strength of their cybersecurity.
These tests are carried out in a controlled environment, meaning there’s no real risk of your systems or data being compromised.
Once the testing is complete, the findings are reported and this data is used to inform decisions about cybersecurity strategy moving forward.
This is an invaluable part of IT security management and risk assessment and gives businesses an insight into how hackers behave.
Gap Analysis
A gap analysis isn’t necessarily always included as a part of the cybersecurity risk audit process, but for many businesses today, this aspect is vital.
Organizations that operate in highly regulated industries, like healthcare, education, and finance, have to abide by evolving regulations revolving around data security. A gap analysis will assess a business’ compliance standards, policies around data management and information security, and enforcement protocols.
After performing a gap analysis, it’s a lot easier for organizations to understand where they stand concerning compliance with data security regulations and receive guidance on any corrective actions that need to take place.
While a gap analysis is most useful for organizations operating in industries with strict data governance rules, it’s important to note that universal standards are being increasingly sought-after and adopted.
Even if you aren’t required to conduct one, doing so will put your business ahead of the curve so you can stay prepared (and avoid spending money to catch up) when local bodies do adopt their own regulation.
Additionally, with the increased sophistication and volume of cyberattacks, more industries are looking to establish data privacy regulations to standardize how data is handled from the moment its generated.
Step 3: Analysis and Reporting
The last phase in a cybersecurity risk audit is rooted in analysis and reporting.
Key insights from the audit will be found in the reporting, which reveals your current cybersecurity strengths as well as where you have vulnerabilities across your network. By taking the time to analyze these reports and sift through the findings, you can make informed decisions that improve your defenses moving forward.
These insights will also allow you to jump into any immediate remediation actions that are needed to address major vulnerabilities while also planning for long-term improvements.
Once these next steps have been presented and discussed, the business can begin implementing cybersecurity measures that substantially improve the network defenses as a whole.
The Importance of Cybersecurity Risk Audits
As organizations expand their digital ecosystems, risk audits offer a needed moment of clarity. They gather scattered insights, confirm what’s working, and highlight where the security strategy may be drifting. Even when an environment feels stable, these assessments reveal how quickly small oversights can compound into systemic weaknesses.
Beyond identifying vulnerabilities, audits help teams reset their priorities. The findings give leaders a grounded view of which risks deserve immediate attention, which can be monitored, and which controls may need refinement. This clarity helps ensure that investments in tools, processes, and people align with the organization’s actual exposure—rather than assumptions about it.
Taken together, regular audits create a rhythm that keeps the broader security program honest and adaptable. They nudge teams to revisit decisions, document changes, and stay aware of how internal and external factors evolve. By the time an audit wraps up, organizations not only understand their risks better, they’re more prepared to address them with focus and confidence.
Wrapping Up on Cybersecurity Risk Audits
Conducting regular risk audits is integral to keeping tabs on your cybersecurity and how it compares to industry standards and best practices.
Not only should your organization look to conduct a cybersecurity risk audit in the near future, these audits should be scheduled on a regular basis so you can understand how your business is evolving rather than operating solely on a point-in-time snapshot. By establishing a risk audit cadence, you can ensure that your efforts are never outdated.
A cybersecurity risk audit will give you the vision into your efforts that you need, but it’s up to you to fill the gaps that are found.
Learn how cybersecurity practitioners go about identifying and responding to live threats in Impact’s webinar, Dissecting Cybersecurity Breaches: How They Happen & How to Stop Them.