April 2020 update: In light of the COVD-19 outbreak, we’ve seen a substantial rise in the number of cyberattacks that have been taking place.
Website registrations and email campaigns relating to the pandemic have soared, meaning that criminals are leveraging the outbreak to victimize unsuspecting users.
Related Post: AI-Generated Malware and How It's Changing Cybersecurity
There are emerging stories of scams losing Americans $13.4 million to fraud, and Google’s claims that they are blocking 240 million spam messages per day related to the virus.
We wrote a blog recently that demonstrates one example of how cybercriminals are tricking users into handing over personal credentials and confidential information.
As you might imagine, the United States is the top location for these types of attacks, and there are no signs of slowing down at present.
Because of these emerging threats, it’s more important than ever that businesses have a clear understanding of the types of attacks they may encounter in the coming months and beyond.
What Is Ransomware?
Keeping abreast with the advances in cybercrime is a demanding task for network security professionals.
If you’re still not sure about what ransomware is, you’ll need to get up to speed quickly with this threat.
With modern tactics and sophisticated malware, cybercriminals target both individuals and businesses using ransomware and can devastate networks and businesses.
Ransomware uses encryption or elevated access controls to block users from accessing their workstations or cloud services.
If an attack succeeds, the victim will need to pay the malicious actor before they can regain access to their system.
Attacks come in many forms, but usually it’s an errant click from a user on an infected link that grants the hackers access.
The Different Types of Ransomware Attacks
The software and tactics used by cybercriminals continue to evolve with technology.
The rise of cloud services and access to sophisticated encryption tools enable bad actors to improve their skills and threaten even the most secure networks.
Earlier methods rely on using access controls to modify passwords using locker malware, locking users out of their systems.
This worked well, but better account recovery options from software and service providers helped users overcome these kinds of attacks.
The latest types of attack are crypto ransomware.
This encrypts files on the user’s system, forcing them to pay the hackers with crypto currency or credit cards to decrypt the files.
Both methods still rely on gaining access to the system, so ensuring you protect your networks is of vital importance.
Related Post: Why a Managed Security Service Provider (MSSP) Is Good for Your Business
7 Dos and Don’ts of Ransomware
There’s a lot you can do to protect from ransomware attacks.
A proactive approach to network and device security is key, but you can also improve your system’s defenses to help you recover if an attack succeeds.
1. Don’t Pay the Ransom
If an attack succeeds, don’t pay the requested ransom.
While this may be the quickest way to regain access, it could make you a regular target.
It will also embolden the attackers, leading them to continue running the same tactic on other businesses and reinvest the money they’ve made from you into their racket.
By not paying the ransom, you reduce the efficacy of the criminal endeavor.
Moreover, there’s no guarantee that paying the ransom will actually solve your problem.
Only one in five victims who pay ransoms get their information back.
2. Restore Your Systems From Backups
You should have a regular backup policy in place that allows you to mitigate ransomware attacks.
Even when an attack succeeds, redoing a few days’ or a week’s worth of work is more desirable than submitting to the extortion.
The better your backup strategy, the better you’ll be able to respond effectively to an attack.
3. Keep Personal Information Out of Emails
Hackers use social engineering techniques to gain access to the network.
Any personal information contained in emails or communications help them craft an attack that’s more likely to succeed.
Ensuring you keep personal information protected during daily workflows will reduce their ability to create a phishing email that looks like it came from a legitimate source.
The average cost of a ransomware attack was $133,000.
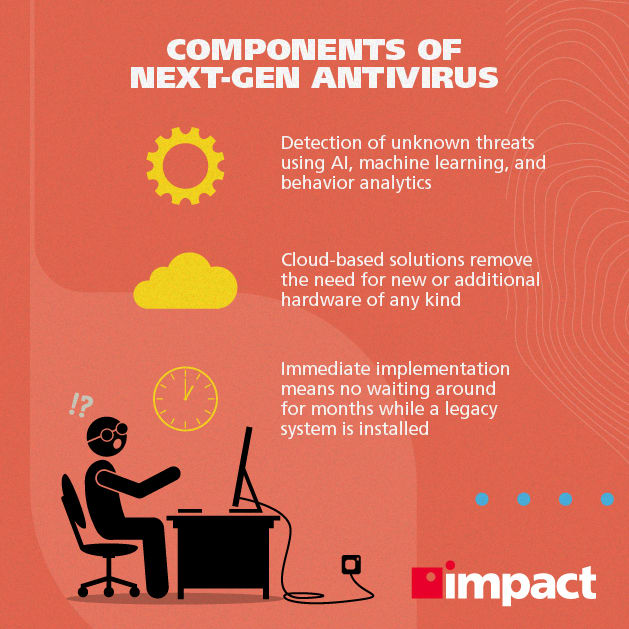
4. Deploy Antivirus and Firewalls on Your Network and Devices
Every company should have a network security policy that uses the latest threat detection technology to ward off an attack.
Firewall definitions include the sites and software cybercriminals regularly utilize for attacks.
If anyone attempts to access these sites from within your network, the system will block the attempt and alert your network security professionals or your IT partner.
5. Invest in Content Scanning and Filtering Solutions for Email Servers
Email is the dominant communication channel between employees and businesses.
As emails can originate from anywhere, ensuring you scan the content and filter out malicious emails before they arrive in the inbox will improve your security.
Content filtering solutions will flag suspicious emails and disable any links they contain.
Ransomware attacks have increased 97% in the past two years.
6. Maintain Security Patching Policies
Ensure you regularly apply the required security patches on all servers, workstations, printers, and other network equipment.
Hackers continually search for exploits in existing systems and strike once they find any vulnerability in a system.
By maintaining a security patching policy as fixes become available, you will drastically reduce the probability of an attack succeeding.
7. Apply a BYOD Policy to All Personal Devices
With more employees now using their own devices to connect to the company’s network, it’s important to include these devices in your BYOD (Bring Your Own Device) security policies.
Using a Virtual Private Network (VPN) whenever employees connect from outside the regular network will ensure your data remains protected.
For mobile devices, the same firewall and end-point scanning rules should apply as any other desktop or laptop device: even the smallest devices are gateways into your system for hackers.
Takeaways for Dealing with a Ransomware Attack
- Backup and encrypt data: Ensure you regularly backup all information (and encrypt backups to protect them from criminals).
- Educate employees: Make employees aware of the daily risks. Highlight the different phishing tactics criminals use and how they can spot suspicious emails.
- Apply security patches: Apply your security patches as they become available on all devices, servers, printers and other networked equipment.
In light of recent events, many organizations have found themselves playing catchup, trying to implement makeshift cloud solutions to make up lost ground while their workforces transition to remote work for the immediate future. Fending off cyberattacks is a challenging but necessary aspect of any modern business, and using cloud services can help create a watertight business. Take a look at Impact’s cyber monitoring services.
To find out more about how the cloud can ensure your business is in good shape for the future, download our eBook, “Which Cloud Option Is Right For Your Business?”