Written by: Isla Sibanda, Cybersecurity Specialist
As the business world continues to move online, the risks of cybercrime are greater than ever. According to Cybersecurity Ventures’ 2022 Official Cybercrime Report, the financial cost of cybercrime is expected to reach $8 trillion this year and $10.5 trillion by 2025, making it one of the biggest threats to businesses worldwide.
Naturally, most business owners will do everything possible to protect their organizations. But, if it does happen, what should a company do after a data breach?
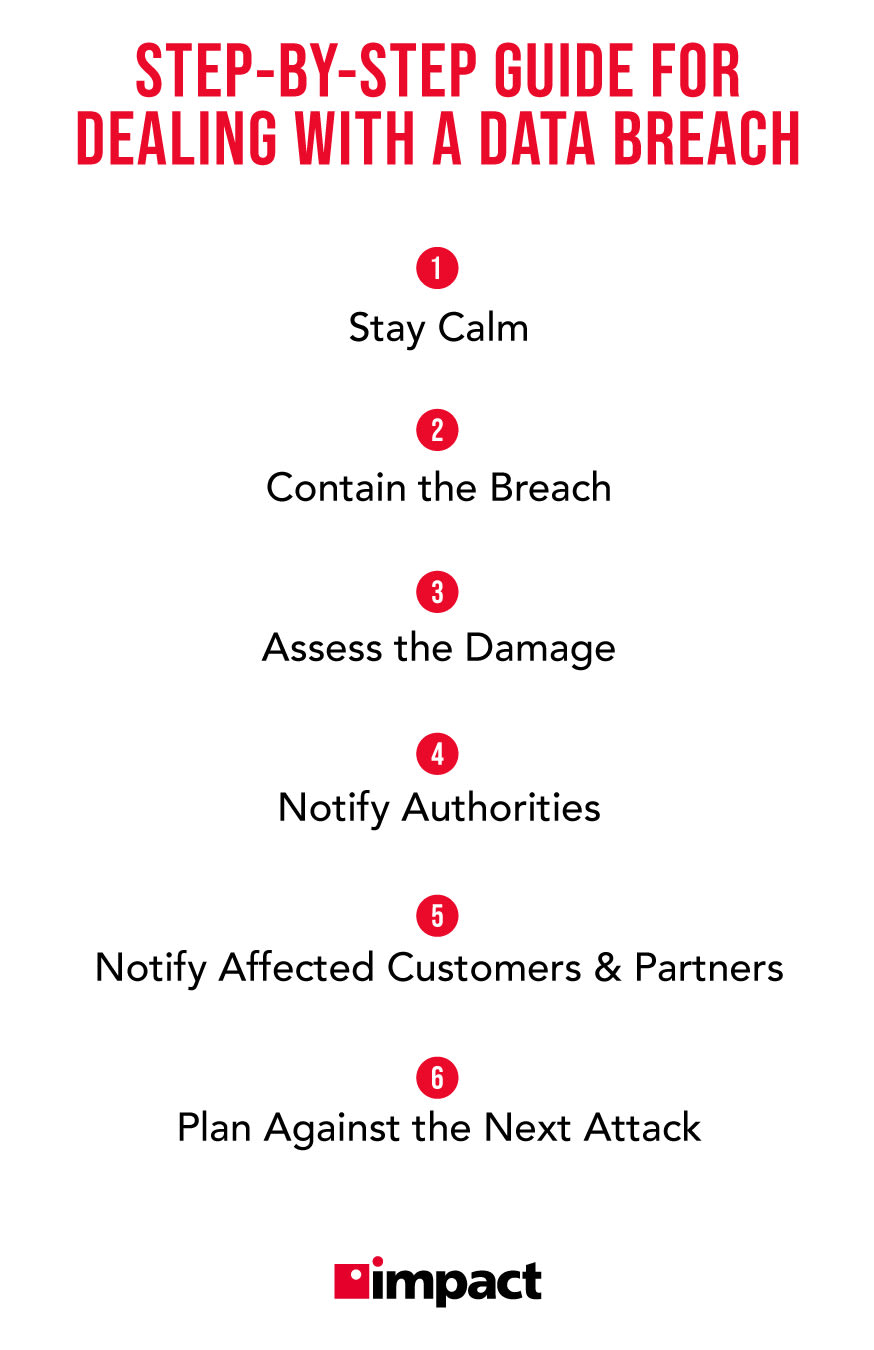
Part of any good cybersecurity strategy is having a plan for remediation in just such an event. This article will explore the key steps you must take when you discover a data breach:
- Stay calm
- Contain the breach
- Assess the damage
- Notify authorities
- Notify affected customers and partners
- Plan against the next attack
Read on to learn more about what goes into each of these data breach remediation steps.
If you’d like to lower the odds of getting breached in the first place, learn how to build an effective, layered defense with Impact’s eBook, What Makes a Good Cybersecurity Defense for a Modern SMB?
The Importance of Taking Action Quickly
The consequences of a successful cyberattack on a business can be severe, long-lasting, and expensive. The average cost of a data breach for a small business was over $17,000 across all countries last year.
Given the high stakes involved, businesses must take action if they have been hacked. What’s most important is that you take action immediately after you realize an attack has occurred. A faster response time will always mitigate the extent of the damage the cybercriminals inflict.
The average time it takes businesses to contain a breach is 280 days, which provides cybercriminals with months to extract company and customer data. On top of that, according to recent statistics, 78% of consumers will take their business elsewhere if they find out a company they’re doing business with has been the victim of a data breach.
This is why taking action as soon as possible to contain a data breach is so essential. But what should a company do after a data breach? Let’s break it down one step at a time.
What a Company Should Do After a Data Breach
1. Stay Calm
In the face of a hack, it’s normal to panic.
However, staying calm will allow you to assess the situation objectively and avoid making rash decisions that could make the situation worse. This way, you can prevent mistakes that could jeopardize the investigation or recovery process.
For example, hastily shutting down systems or deleting data could destroy valuable evidence that could be used to identify the hackers or prevent future attacks.
In addition, staying calm can help you communicate more effectively with your employees, customers, and other stakeholders. By presenting a confident and reassuring demeanor, you can instill trust and credibility and demonstrate your commitment to resolving the situation.
Ultimately, staying calm is a crucial element of effective crisis management. So take a deep breath, gather your team, and remember that you can overcome this challenge with the right approach and mindset.
2. Contain the Breach
Once you’ve discovered a hack, the next step is to contain it. This means preventing the hacker from causing further damage to your systems or data. The longer the breach goes unchecked, the greater the potential for harm.
First, isolate the affected systems and devices to contain the breach, disconnecting them from the network and shutting them down if necessary. This will help prevent the hacker from using these systems to access other parts of your network.
Next, identify the source of the breach and patch any vulnerabilities that allowed the hacker to enter to reduce the likelihood of future breaches. Also, changing all passwords and credentials can prevent the hacker from using stolen credentials to access your systems and data.
By containing the breach quickly and effectively, you can limit the damage caused by the hack and prevent the hacker from causing further harm.
3. Assess the Damage
Another crucial step is assessing the damage already caused by the hack. This will help you understand the extent of the resources you’ll need to restore your systems and data.
First, identify what has been compromised. Determine whether any sensitive or confidential information was accessed or stolen. Check for any changes or deletions of data and assess the impact of any disruption to your systems.
Once you’ve found the scope of the damage, you can begin to develop a plan to address it. This may involve repairing or replacing hardware and software, restoring data from backups, or implementing new security measures to prevent future attacks.
It’s important to involve all relevant stakeholders in the assessment process, including IT staff, management, and legal advisors. That way, you can ensure that all aspects of the damage are identified and addressed appropriately.
By assessing the damage thoroughly and accurately, you can develop a comprehensive plan to recover from the hack and prevent similar incidents from happening in the future.
4. Notify Authorities
If your business has been hacked, it’s important to notify the authorities immediately. This will help you protect your data and systems and assist law enforcement agencies in identifying and prosecuting the hackers.
When notifying the authorities, provide as much information as possible about the hack, including the date and time of the incident, the type of attack, and any evidence you’ve gathered. The information you provide will help law enforcement agencies investigate the incident and take appropriate action.
It’s important to involve your legal team when notifying the authorities to ensure that the notification is made correctly and that your business complies with all applicable laws and regulations.
Remember that notifying the authorities is often a legal requirement as well as a responsible and ethical action. It demonstrates your commitment to protecting your business and customers from cyber threats and can help prevent similar incidents.
By working closely with law enforcement agencies, you can increase the chances of identifying the hackers and bringing them to justice. So don’t hesitate to notify the authorities if you suspect your business has been hacked.
5. Notify Affected Customers and Partners
Your partners and customers also have a right to know about the incident and how it affects them. Notifying your partners will help them take appropriate action to protect themselves and their data and can help preserve their trust and confidence in your business.
When notifying affected customers and partners, provide clear and concise information about the hack, including what data was affected and what data breach steps you took to address the situation. Be transparent about what happened and provide as much information as possible.
For example, you can tell customers if the breach might affect their financial information saved in your system and assure them that you have taken the necessary steps to protect their data in the future. You can also explain how their data was protected before the breach and how you think the hackers gained access.
For instance, your business might have already been PCI compliant and following all the requirements set by the PCI-DSS standards, but the hackers were able to get access to employee credentials through a social engineering hack.
It’s also important to involve your legal and public relations teams when notifying affected customers and partners to ensure that the notification is made correctly and that your business complies with all applicable laws and regulations.
6. Plan Against the Next Attack
If your business has been hacked, planning against the next attack is important. This will help you prevent similar incidents from occurring in the future and protect your data and systems from cyber threats.
When planning against the next attack, take the information you’ve already gathered about the vulnerabilities the hackers exploited. Use it to develop a comprehensive cybersecurity plan that includes regular vulnerability assessments, employee training, and incident response procedures.
You should also involve your IT and cybersecurity teams when planning against the next attack to ensure the plan is comprehensive and effective. Consider working with a third-party cybersecurity provider to strengthen your defenses and provide ongoing monitoring and support.
As a business, you need a strong cybersecurity strategy. Foster a cybersecurity awareness and accountability culture throughout your organization, and encourage all employees to be vigilant against cyber threats.
Also, remember that cyber threats are constantly evolving, so it’s important to stay vigilant and proactive in your cybersecurity efforts.
Bottom Line
As a business owner, the thought of a cyberattack may seem daunting and overwhelming. However, knowing what to do after a data breach can make all the difference in minimizing the damage and protecting your business.
The first priority is to stay calm and act quickly. Contain the breach by disconnecting affected devices from the network and notifying your IT department. Assess the damage by determining what data has been compromised and what actions must be taken.
Then, you must notify the authorities, affected customers, and partners as soon as possible to mitigate the breach’s impact.
But that’s not all. After you’re done containing the damage, planning against the next attack is crucial. It’s important to strengthen security measures, implement incident response procedures, regularly update software and systems, and educate employees about cybersecurity best practices.
Don’t wait until you fall victim to cybercrime – take action today.
Learn more about what actions are the most relevant for your organization and what needs to go into implementing them in Impact’s eBook, What Makes a Good Cybersecurity Defense for a Modern SMB?
Isla Sibanda is an ethical hacker and cybersecurity specialist based out of Pretoria, South Africa. For over twelve years, she has worked as a cybersecurity analyst and penetration testing specialist for several reputable companies, including Standard Bank Group, CipherWave, and Axxess.