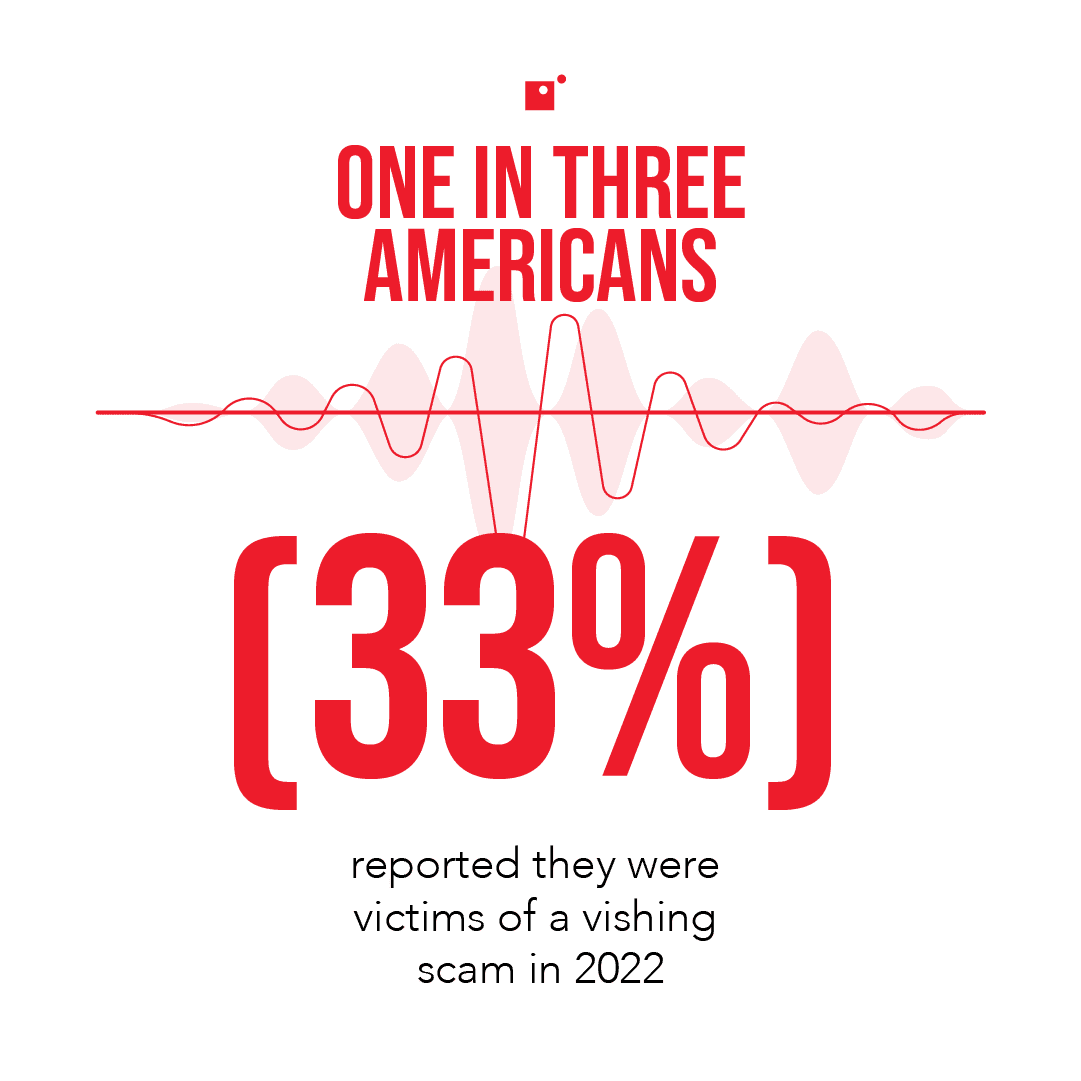
Vishing is a new-aged cyberattack that makes use of phone calls and other smartphone communications to dupe victims. Modern cyberthreats are more sophisticated than their rudimentary predecessors. This means they’re more dangerous, and that there is a wider variety to defend against. So, what is vishing exactly and how does it work?
Vishing is incredibly similar to phishing and the two cyberattacks share the same goal: compromising personal or financial information. It’s worth noting here that this is the goal of most cybercrime in today’s day and age.
In fact, cybercrime has steadily increased over the last several years and this trend is projected to continue into the future. Cybersecurity Ventures even projects the annual cost of cybercrime to increase 15% year over year between now and 2025, reaching a height of $10.5 trillion at the end of that run.
Because there’s simply so much money in cybercrime, it’s not going away any time soon. However, by staying aware of the most recent cybercrime trends, keeping your staff educated, and investing in the appropriate tech, you can keep your network safe and secure against most cyberattacks.
To learn more about modern cyberattacks and what you need to defend your network against them, watch Impact’s webinar, Dissecting Cybersecurity Breaches: How They Happen and How to Stop Them.
What is Vishing?
Vishing makes use of fraudulent phone numbers, voice alterations, and social engineering in order to dupe the victim(s) into giving away sensitive information. That makes it very similar to phishing, and the two cyberattacks share similar goals.
The visher will use their fraudulent phone numbers to call potential victims, pose as authority figures (the IRS is a popular one) or even use AI to make their voice sound like that of the victim’s close friends or family, and then berate them with fear tactics until they’ve gathered the information they were after or made off with a substantial wire transfer.
Vishing is rarely used by its lonesome, though. It’s much more likely that scammers use vishing in concert with smishing and even social engineering tactics in order to launch potent large-scale cyberattacks.
How Vishing Works with Smishing
Vishing is all about the actual phone call. Smishing, on the other hand, is rooted in texting. This is important because scammers will start their attack with a malicious text (smishing) that includes a phone number.
If the victim calls that number, they’re directed to the scammer who will refer to the messaging in the text and attempt to leverage payment. Scammers like to pose as governmental agencies (like the IRS) because they know there’s a general air of fear around getting in trouble with the law.
Preying on this fear, vishers work their victims from multiple angles in order to steal credentials, finances, or both.
Vishing with Robocalls
If a vishing attack isn’t mounted in concert with a smishing counterpart, the scammer might be using an automated dialing program to call phone numbers in massive volume. These robocalls, as they’re known, deliver computer generated voice messages that lead the victim down a journey designed by the hacker.
These automated computer messages are meant to build trust with the victim and to lead them into a false sense of reassurance. Once they’ve hit a certain point in the path, the computer will transfer them to the actual hacker to finish out the scam, or might direct the user to a compromised website.
Deep Fakes
Since vishers don’t want their victims to suspect anything, they often will use a variety of tactics to mask their identity. In some cases, they will even go as far as impersonating someone that you know personally.
This can be done with sophisticated voice-altering technology that is often powered by AI, and is a really nasty way to manipulate people into giving up their credentials, transferring money, or revealing other personally sensitive information about themselves.
Deep fakes are slightly less common than standard vishing attacks because of their sophistication and the technology and time required. That said, they’re also harder to identify and easier to fall for because of the compelling and often urgent nature of the material being faked.
Where Does Phishing Fit In?
We’ve mentioned phishing several times throughout this article; which is essentially a blanket term. In other words, vishing and smishing attacks are specific forms of phishing. Traditional phishing attacks are launched through emails and oftentimes target a specific organization. Since vishing and smishing are forms of phishing, it makes sense then that these three attacks share the same goal.
Traditional phishing scams come in the form of fraudulent emails that contain malicious links and compelling copy. The goal for a phisher is to get a victim to click on one of the malicious links or attachments in the phishing email.
Depending on the type of attack, this can result in compromised credentials, or in a worst-case –scenario, ransomware being downloaded onto the device.
While phishing, vishing, and smishing differ in their delivery medium, all three of these social engineering attacks are designed to compromise sensitive information and to steal money.
How to Identify Vishing
Luckily, there are a few telltale signs that a scammer is trying to vish you. First and foremost, you should check the number associated with any suspicious or unfamiliar text messages. Most of the time, you’ll notice these caller IDs have an invalid format, containing only 4-6 digits.
While telecom systems use this format, it can also be indicative of a message that was sent from an email address, an API, or an auto-dialer. While this doesn’t guarantee it’s a vishing attempt, it should raise some red flags. Especially if the content of the message itself seems out of the blue, random, or much too urgent.
In this same vein, vishing, smishing, and phishing all rely on fear tactics. High-pressure and high-urgency messaging can also indicate a vishing attempt.
Finally, the best defense against vishing is to be aware and simply ignore texts and calls from unknown numbers, report them as spam, and only return a call to an unknown number if they’ve left a legitimate voicemail.
Wrapping up on Vishing
Vishing is one of the more modern forms of social engineering and stems almost completely from phishing techniques. The main difference between vishing and phishing is that one makes use of fraudulent calls and texts, while the other uses a fake email campaign to dupe victims.
Staying aware of modern cybersecurity threats and knowing how to identify them is incredibly important to protecting both personal and company information.
By committing to and investing in a comprehensive cybersecurity posture, you can greatly reduce the risk of social engineering scams infiltrating your organization.
Cyberattacks are only going to continue evolving as technology advances. Get ahead of the game by watching Impact’s webinar, Dissecting Cybersecurity Breaches: How They Happen and How to Stop Them.