If you’re looking to secure your business network, you may have heard of domain name system (DNS) layer security. DNS layer security is crucial in neutralizing threats before they even have a chance to attack.
In short, DNS layer security is a pivotal aspect of a comprehensive cybersecurity strategy that involves protecting devices and users by controlling the transfer of information between user devices, routers, and the internet at large.
With an understanding of how DNS layer security works, and the core principals at play, you can make a well-informed decision about the specific DNS layer security solution that fits your business needs and keeps your network, devices, and users safe.
For a deeper look into cybersecurity incidents and how experts respond, watch Impact’s webinar, Dissecting Cybersecurity Breaches: how they Happen & How to Stop Them.
DNS Explained
The Domain Name System is a logging convention that is used to facilitate communication between individual devices and the internet at large. This system uses IP addresses, or internet protocol addresses, to create an address book of sorts for both devices and websites.
The DNS uses IP addresses to create a connection between devices accessing the internet and the specific piece of the internet being accessed.
For instance, if you visit our website by typing the URL www.impactmybiz.com into your browser, you’re actually using the DNS, which translates that request into computer-friendly language that ensures the proper website is loaded on your device.
This process happens through a series of phases that includes four different DNS serves that all facilitate a different part of the journey.
- DNS Recursor: The DNS server recursor receives the original request from the device and is tasked with creating additional queries to retrieve and deliver the requested website.
- Root Nameserver: The root nameserver is next in line, and is responsible for pushing the specific query further down the line to a more specific location for the requested domain.
- Top-Level Domain (TLD) Nameserver: The TLD nameserver directs queries based on the end of the URL (.com, .edu, .gov, etc.).
- Authoritative Nameserver: This is the last step in retrieving and delivering a device query through the DNS. The authoritative nameserver will find the exact location of the requested site and return that information to the DNS recursor which then loads the website onto your browser.
Each level of the DNS hierarchy (recursor, root, TLD, and authoritative servers) plays a critical role in ensuring that domain names are resolved accurately and efficiently. This system is essential for the usability of the internet, as it seamlessly connects user-friendly domain names with the numerical IP addresses necessary for network communications.
DNS Layer Security
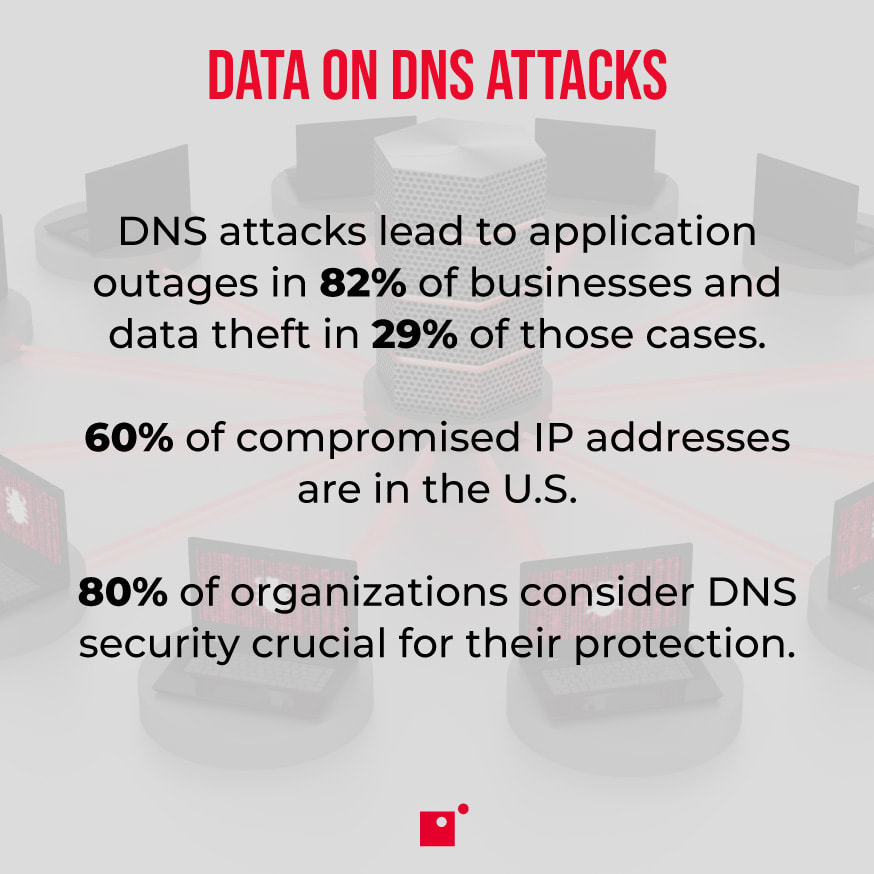
The DNS is a crucial component of the internet, translating human-readable domain names into IP addresses that computers and network enabled devices (like IoT tech) use to communicate with each other. Given its fundamental role, the DNS is a prime target for cyberattacks, such as DNS spoofing, cache poisoning, and distributed denial-of-service (DDoS) attacks.
DNS layer security aims to safeguard the integrity, confidentiality, and availability of DNS information and ensure reliable and secure internet connectivity.
Key strategies of DNS layer security are the use of DNS filtering, Domain Name System Security Extensions (DNSSEC), monitoring, and analytics.
- DNS Filtering: This strategy blocks access to malicious domains by comparing requested domain names against a list of known threats.
- DNSSEC: This strategy adds a layer of authentication to DNS responses, ensuring that users are directed to legitimate websites by digitally signing data to prevent tampering.
- Advanced Monitoring and Analytics Tools: These tools help detect and respond to abnormal patterns and potential threats in real-time, enhancing the overall resilience of DNS infrastructure.
By implementing these measures, organizations can significantly reduce the risk of DNS-based attacks and improve their cybersecurity posture.
How Can You Protect Your Company With DNS Layer Security?
Your computer connects to DNS servers as the first step of visiting websites, making this the first and best opportunity to stop a threat in its tracks.
For example, say you have no protection at the DNS layer. This means that your computer will happily connect to DNS servers and websites regardless of their potential dangers because there is nothing to indicate they may be malicious.
This is how end users connect to suspicious websites, and they can subsequently be attacked and infected by clicking on elements of that website designed to infect computers. With a cloud security gateway like Cisco Umbrella at the DNS layer, sites are inspected at the source and users can be blocked from visiting websites that are found to be malicious.