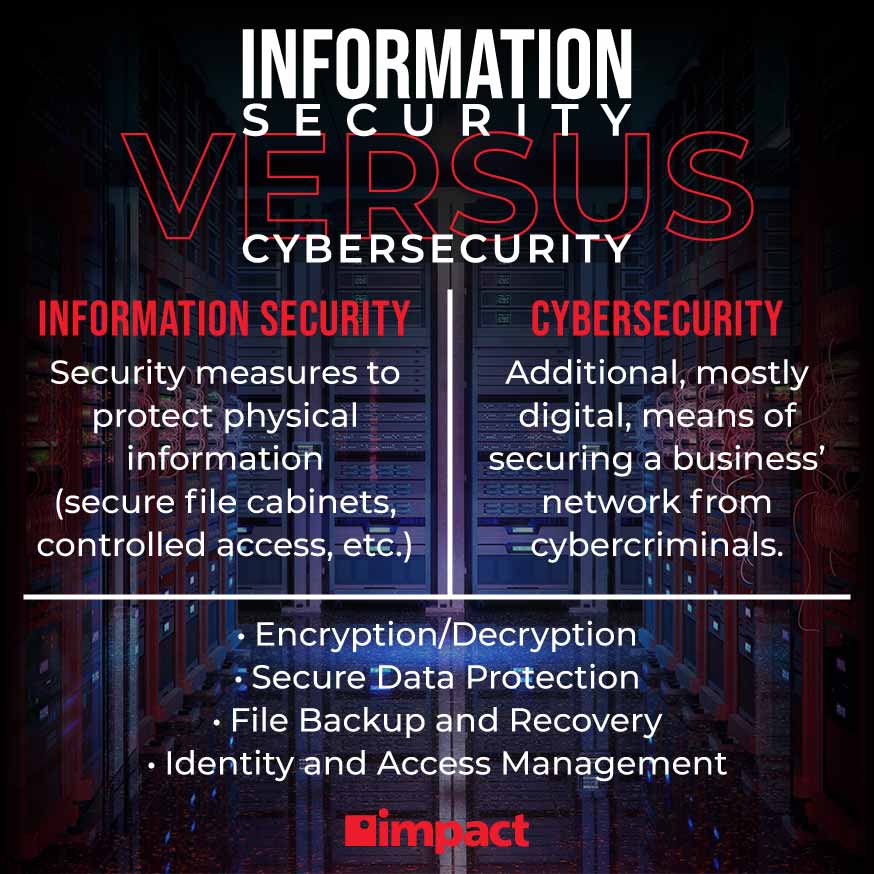
Is information security a subset of cybersecurity? Information security and cybersecurity are independent, but they overlap in key areas. Essentially, picture it like a Venn diagram. For example, encryption is both a part of cybersecurity and information security, but information security also involves the physical protection of documents which is not covered in cybersecurity.
Cybersecurity
Is Information Security a Subset of Cybersecurity?
Is information security a subset of cybersecurity? Infosec is an important part of any tech stack. Find out more here.
Blog Post
5 minutes
Oct 07, 2022
Why is Information Security Important?
It goes without saying that protecting data from unauthorized access—namely cybercriminals—is important for businesses today.
Why? Because the average cost of a data breach is rising. In 2021, it was $4.24 million, in 2022, it increased to $4.35 million (a 2.6% increase). But it’s not just potential financial loss that businesses should be worried about, it’s also the losses in customer and employee trust which can lead directly to lost business. 81% of consumers would stop engaging with brands if their data was stolen due to a data breach.
The importance of strong information security is made clear by the potential financial and reputational harm that could be caused by a data breach where sensitive information is lost or stolen.
Along with these risks, information security is becoming more and more important as time goes by, thanks to these three trends in modern business:
1. Data Breaches are Becoming More Frequent
Firstly, cyberattacks have risen significantly in recent years as more people and companies adopt digital technology and the number of attack vectors increased for hackers.
This has led to a surge in cybercrime—even without the impact of COVID, which brought with it a substantial investment among many in new digital tech creating new targets susceptible to attack.
According to Cybersecurity Ventures, a cyberattack incident will occur every 11 seconds in 2021. This is nearly double the rate in 2019 (19 seconds), and four times what it was in 2016 (40 seconds).
Cybercrime has increased at a rate of roughly four times over the last five years alone—a source of significant concern for businesses and those in the cybersecurity industry.
In particular, data breaches are becoming more common with 75% of firms in the US reporting they experienced one last year that disrupted their business, 43% of which were small businesses.
2. Businesses Are Investing More in Technology
As the costs of software-as-a-service and other tech solutions have decreased, the barrier for entry for digital transformation and a desire from businesses to be more forward-thinking in their approach to technology has fostered a business environment which is investing heavily in technology.
For example, public cloud spending increased 6.3% in 2020, and 44% of businesses indicated that they had already accelerated or planned to accelerate their digital transformation efforts. By 2025, there will be 100 zettabytes (1 billion terabytes or 1 trillion gigabytes) of data stored digitally via the cloud. For cybercriminals, that’s ripe for the taking, especially because credentials, records, and other data are fetching more than ever before with some data, like medical records, selling for thousands of dollars.
3. The Rise of Social Engineering Attacks
As much as cybersecurity has come a long way with regard to modern solutions using automation and machine learning, human error is still an issue that causes a disproportionate number of breaches among organizations. Cybercriminals are preying on people’s lack of security intuition, training, and awareness to trick them into clicking on malicious links, downloading viruses, and exposing their login credentials, giving hackers a gateway into a business’ network.
Attacks such as phishing scams have become widespread over the course of 2020 and beyond. With 98% of modern cyberattacks involving some sort of social engineering, it’s become crucial for businesses to implement security help for their employees to aid them in identifying and avoiding risks, using tactics like:
- Consistent cybersecurity awareness training and education in the form of in-person classes, digital courses, certifications, and hands-on experiences
- Better firewalls and antivirus software to help filter out malicious content
- Encrypt all information being sent and shared
- Implement strong credential and access protocols like password management and multi-factor authentication
Human error is the foremost cause of data breaches, with as many as 52% of breaches being directly attributable to employees falling for methods like phishing, but with proper security procedures in place, most of these risks can be avoided or mitigated to limit the damage caused by human error.
Information Security in a Layered Cybersecurity Strategy
To improve their information security, organizations should adopt a layered approach to their cybersecurity. Using tactics like encryption, education, access controls, network monitoring solutions, and the best antivirus and firewall software, businesses can prepare themselves for all modern threats to their data security. In a layered security approach, information security acts as one of several solutions that make up a quality stack.
The solutions within a layered cybersecurity strategy work together to boost all the necessary areas of security, including infosec, elevating the security across your organization, and protecting all your data, processes, people, customers, and more.

In Conclusion: Information Security vs. Cybersecurity
Is information security a subset of cybersecurity? The answer is: it’s complicated.
Information security is a part of a larger cybersecurity strategy, but certain aspects of it stray from cybersecurity, such as physical document security, facility access strategies, and more. But, it’s important to understand where the two overlap when protecting digital information.
In cybersecurity, information security means protecting customer data with secure login credentials and password management, having protocols in place for access management, and encrypting information to keep it safe from prying eyes and cybercriminals who would steal or destroy it.
Learn more about information security’s role in a larger, layered cybersecurity strategy in our blog, Why You Need Layered Security, to see why businesses need to take the necessary steps to implement full, layered security to protect themselves from modern threats.
Impact Insights
Sign up for The Edge newsletter to receive our latest insights, articles, and videos delivered straight to your inbox.