Hardening network security has become an increasingly important aspect of business operations for most organizations.
For the last several years, the number of cyberattacks targeting SMBs in particular has changed the way organizations approach their security and the way they prioritize technology investment.
As you can imagine, much of this investment has been in tools and solutions that focus on hardening network security and preventing data breaches.
Managed security services are the most common demand for SMBs today, receiving more investment (20% market share) than any other cybersecurity market (Network security, 16%; Integration services, 14%).
In this blog, we’re going to talk about what hardening network security means and what needs to be done to ensure malicious actors have as few opportunities as possible to infiltrate a business network.
What Does Hardening Network Security Mean?
When we talk about hardening network security, we’re talking about reducing what is referred to as an “attack surface” so that bad actors have the smallest chance of gaining unauthorized access to a network environment.
Cybercriminals essentially operate with a law of averages approach to their campaigns.
They know that not all of their attacks will work, and they know that many of the businesses they target will quite effortlessly defend themselves because they have the correct security protections in place.
They also know that if you were to take a random sample of businesses, at least one of them will have limited protection and be susceptible to cyberattacks.
As far as the hacker is concerned, they will keep sending attacks (be it via phishing or some other method) until someone is breached, because sooner or later one of their attacks will target an organization that is unsecured.
Endpoints vs. Embedded Devices
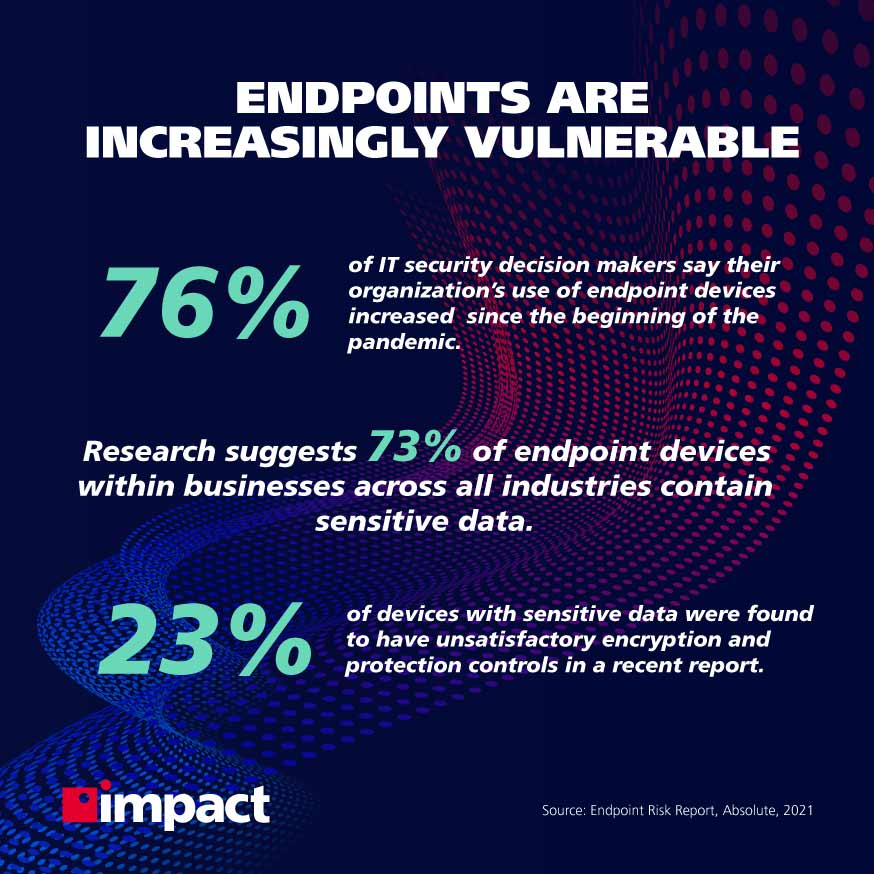
Traditionally, cybercriminals and hackers have sought to target conventional endpoints, which can generally be thought of as devices like laptops and computers.
However, because of the rise of the Internet of Things (IoT) and the volume of associated devices that now exist and are connected to virtually every network, the focus has shifted in a large way.
In 2015, there were an estimated 3.6 billion connected IoT devices worldwide. In 2020, that figure was 11.7 billion and by 2025 is expected to hit 30.9 billion.
With the number of devices now present in every company’s network, hackers have turned their attention to targeting embedded devices.
These are devices that are typically specialized and often small. Examples of common embedded devices in an office setting would be a switch, router, sensor, and sometimes things as unsuspecting as a thermostat.
Security Recommendations for Businesses
There are several recommendations to make in order to harden their network security.
Many of the ones in this blog are taken from the NSA’s recommendations on hardening network devices.
General Security Recommendations
Because there are so many ways to access devices on a network, it’s recommended that organizations take certain precautions in order to reduce their attack surface and protect themselves from malicious actors.
- Ensure the latest OS version on each device is installed and up to date.
- Patches that are installed should be tested so that stability is maintained.
- Enforce a security policy for all devices connected to the network.
- Backup configuration files.
- Do not share configuration files using unsecured means.
- Disable unused services and implement access controls for active services.
- Perform periodic security tests for network devices and compare their configuration against the original configuration to verify them.
Access Control Recommendations
Poor or no access controls are key reasons business networks are compromised.
Bad actors can gain access to a network through several vectors, like a virtual terminal connection, administrative connection, auxiliary line, or console line.
The following recommendations for access controls are advised:
- Use multi-factor authentication.
- Use out-of-band management to divide network admin and user traffic.
- Restrict access to the console port.
- Limit simultaneous management connections.
- Utilize the strongest encryption available on IoT devices on the network.
- Apply IP address access control lists to reduce the risk of exposing admin interfaces to user traffic.
- Restrict physical access to routers and switches and apply access controls for remote access.
- Monitor and log all attempts to access network devices.
Source: NSA
Understanding and Remedying Vulnerabilities
Following these recommendations is a great way of hardening your network security and reducing the chances of being infiltrated.
For many businesses, getting a handle on exactly what devices they have in their network and what their key vulnerabilities are is the best way to know what needs to be done.
This is where vulnerability scanning and penetration testing are extremely valuable for modern organizations.
The services of a managed security service provider (MSSP) are useful in this regard. They will conduct a risk audit, which uncovers vulnerable endpoints in the network while also using white-hat hackers to perform mock penetrations and act the part of a hacker to determine the most likely avenues of attack.
How Do Solutions Play a Part?
Once a business has an understanding of what its risks are, it can begin to implement the necessary changes to protect itself and start hardening network security in its business.
Many of the recommendations above will typically be performed by an internal IT or cybersecurity specialist or a third-party (usually an MSSP).
The solutions adopted will depend on the needs of the organization, but since the main area of focus with network security is endpoints, a typical solution, in this case, will be mobile device management (MDM).
MDM is a security solution that can be used to remotely monitor every device in a business’ network and ensure they are correctly provisioned and patched.
Once the appropriate solutions have been adopted, it’s a case of implementing rules and policies for management and data governance, which should be overseen by a dedicated member of staff or third-party security specialist.
Bottom Line
Hardening network security is an important aspect of cybersecurity for a modern business.
With the number of Internet of Things devices connected to modern networks, as well as remote workers accessing these networks, the opportunities for malicious actors to exploit vulnerabilities are greater than ever.
In order to combat these threats, companies must be implementing network security monitoring services and solutions to the best of their ability. The best way to do this is to have a risk audit conducted to understand vulnerabilities and have an expert lay out a strategy for solution and policy implementation, as well as ongoing support for business security.
If you need cybersecurity but are unsure where to start, consider having a risk audit done by Impact. Get started today to get the ball rolling on securing your future.